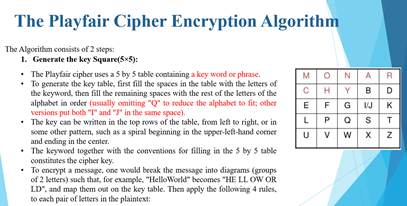
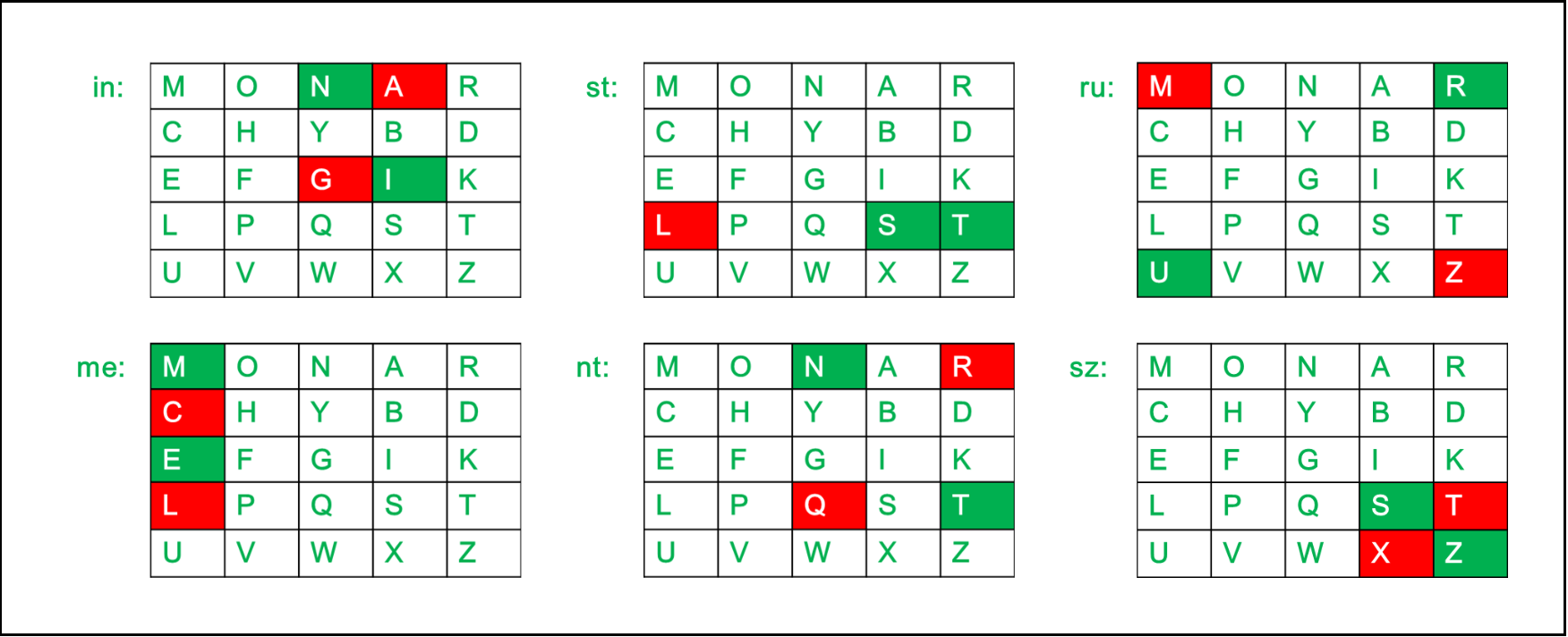
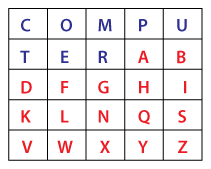
PLAYFAIR CIPHER WITH EXAMPLE||SUBSTITUTION TECHNIQUE||MATHEMATICS OF CRYPTOGRAPHY-- NETWORK SECURITY - YouTube

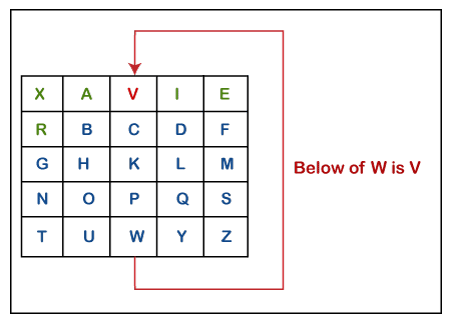
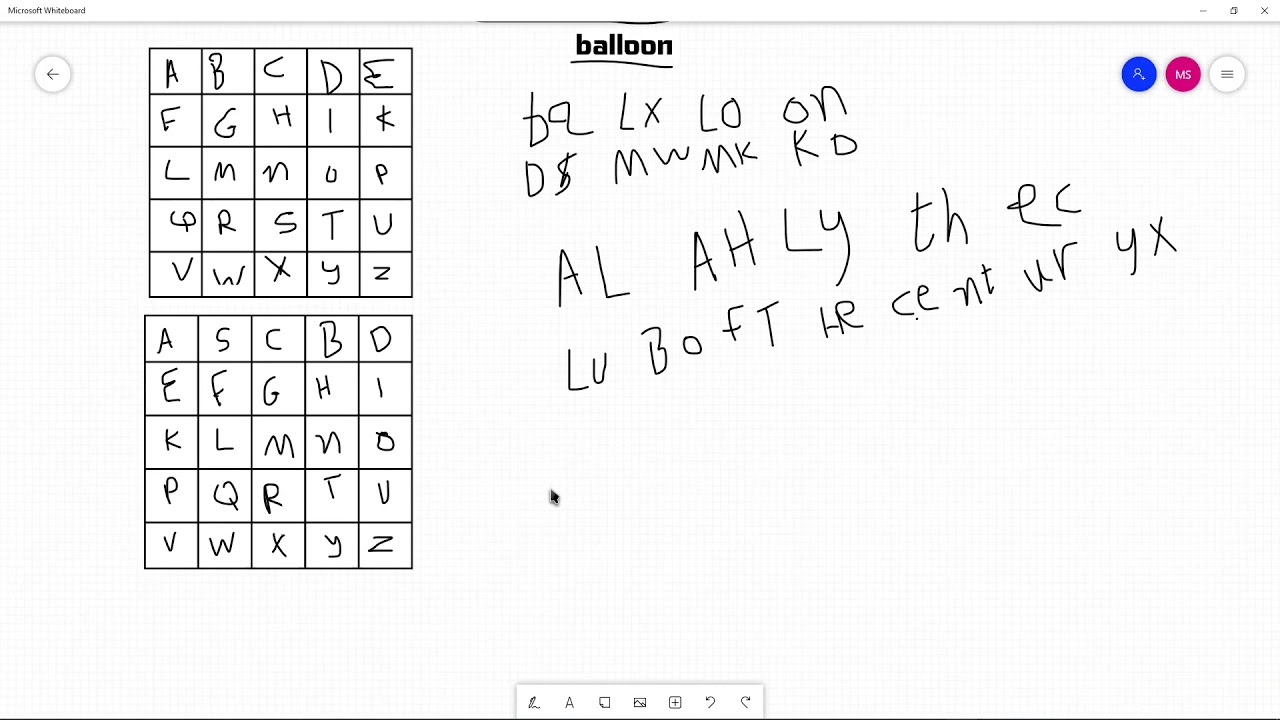
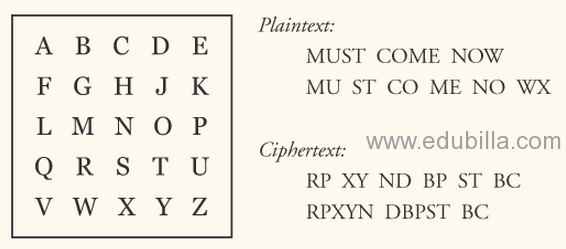
Playfair Cipher in network security | Playfair Cipher example | Playfair cipher encryption - YouTube

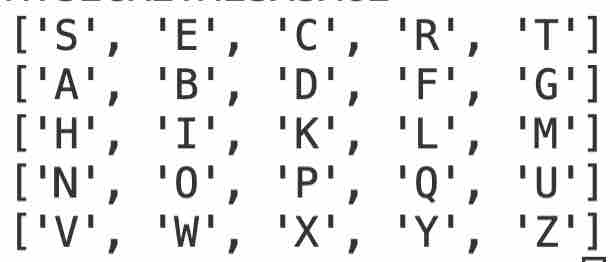
Running Key Cipher The security of polyalphabetic substitution cipher reside in key length. In running-key cipher, the length of key must be equal the. - ppt download