.jpg)
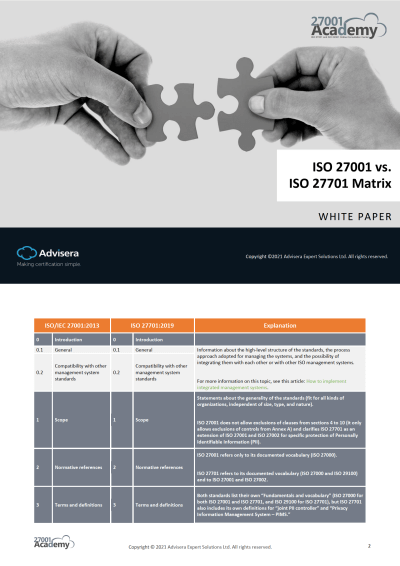
INCITS/ISO/IEC 27001:2013/COR 1:2014 (2019) - Information technology Security techniques Information security management systems Requirements - Technical Corrigendum 1
![PDF] An Approach to Map COBIT Processes to ISO/IEC 27001 Information Security Management Controls | Semantic Scholar PDF] An Approach to Map COBIT Processes to ISO/IEC 27001 Information Security Management Controls | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/4d69c7653470b94e6a0818f92eb9e706e82b5608/10-Table2-1.png)
PDF] An Approach to Map COBIT Processes to ISO/IEC 27001 Information Security Management Controls | Semantic Scholar









![PDF] ISO/IEC 27000, 27001 and 27002 for Information Security Management | Semantic Scholar PDF] ISO/IEC 27000, 27001 and 27002 for Information Security Management | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/444e8aacda5f06d2a6c5197c89567638eaccb677/8-Table3-1.png)